The desire to explore restricted destinations has always tempted people to devise every possible way to break those rules, be it in the real world or in the virtual world.
In the wake of such a fact, the world of the internet is no different with various countries imposing their own censorship editions.
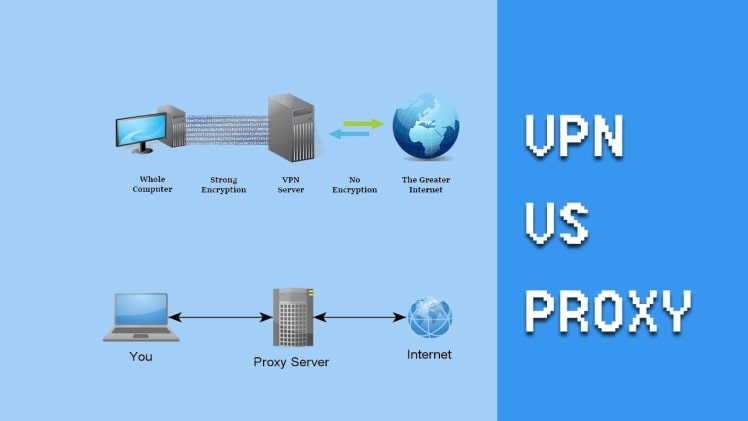
As expected, there are varied ways to maneuver these restrictions as well with VPN and proxy servers being the pick of the masses.
However, choosing one of them on the basis of superiority is indeed a moot point. Though, if you have a look on all the pros and cons of these filtering bypassing methods. VPN is supposed to have a cutting edge over proxy servers. Why? Let’s know by starting with their definitions first.
What is a proxy server?
Also known simply as Proxy, a proxy server acts as an intermediary computer to fulfill the requests of clients on some other computer.
In simple words, the client establishes a connection to the proxy server with the intention to request some specific services such as the opening of a webpage, downloading a file, or creating a connection with a different server.
For example, if you are unable to open Facebook from your current location then in order to bypass the filtering, you can browse through any of these residential proxies websites, enter the Facebook URL and start accessing it.
Here these servers act as intermediary computers and abide by your request.
Some of the Best Proxy providers in the industry are Hidemyass Proxy and Cyberghost Proxy.
What is a VPN
VPN keeps you completely anonymous and allows you to access the blocked websites. The network is thus created over a public internet connection by establishing an encrypted tunnel between the client and the destination servers.
In short, you can say that it is the emulation of a privately owned local network over the internet via a public network. Alongside enabling you to access restricted websites, it promises much more facilities such as high degree security, intrusion-free network, appreciable speed, and so on.
To cite an example, if you want to open Hulu from outside the US which is otherwise only available in the US, a VPN comes in handy and allows you to explore it without getting into the hit list of the owners.
Comparing Proxy and VPN:
Putting aside both the Proxy server and the VPN, you will notice that VPN holds an upper hand over the latter due to following reasons:
1. Security
- A proxy server caches the data that you use to access the websites. Though, this increases the browsing speed but only at the cost of losing your sensitive credentials. The owner of the proxy server can access all the information including the browsing history, username, passwords, and more, and can use them for some unsolicited purpose.
- A VPN, on the other hand, assures you due security from breach of privacy and allows you to access the websites in total anonymity.
2. Intrusion
- With a proxy, there is always the chance of your network being intercepted. Hence, no wonder if you are using even some anonymous proxies on SSL /TLS encrypted connections; you can always be intruded on by hackers.
- With capable VPN protocols, however, you can rest assured to a great extent from such kind of intrusion. You can opt for the protocols that could provide you with the best of facilities with due consideration being given to your privacy.
3. Reliability
- Sometimes, proxy servers cannot be of much help in allowing you to open blocked websites, especially if you are in the Middle East, China, or some other heavily censored country. Your computer would be tracked within no time and you would be dealt with accordingly on the charges of accessing the restricted part of the internet.
- Thankfully, with a VPN you can save yourself from indulging in any such problem. VPN protocols such as SSH, PPTP, L2TP, and more enable you to hide your identity from the censoring authorities and hence emancipate you from getting into legal hassles.But make sure that you do it carefully even in the case of VPN and use only the protocols that have been undetected so far in that particular area.